New: SSL Certificate Monitoring, Security Center, Domain & SSL Expiration Tracking - Plus Our Affiliate Program
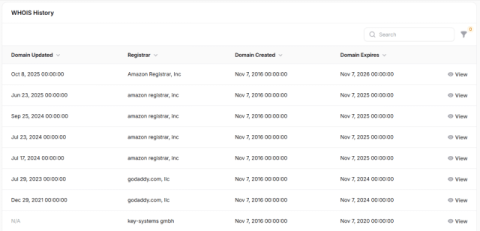
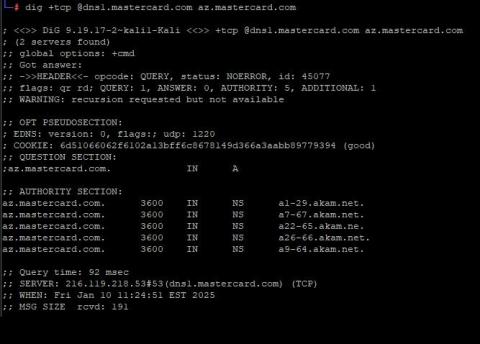
DNS Spy now goes well beyond DNS record monitoring. We've shipped SSL certificate discovery and security auditing, expanded the Security Center to 40+ automated checks across six categories, and built expiration tracking for both domains and SSL certificates — with tiered alerts so nothing expires without warning.