How to Secure the network of your GKE Cluster
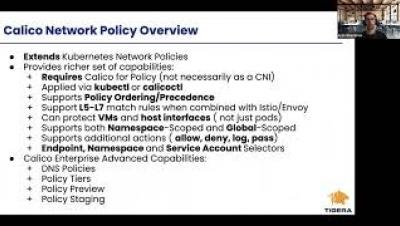
By default, pods are non-isolated; they accept traffic from any source. The Google GKE solution to this security concern is Network Security Policy that lets developers control network access to their services. Google GKE comes configured with Network Security Policy using Project Calico which can be used to secure your clusters. This class will describe a few use cases for network security policy and a live demo implementing each use case.