Operations | Monitoring | ITSM | DevOps | Cloud
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Why Choice and Control Matters with Observability and Security Data
“We lost choice and control when we migrated to Splunk Cloud, but got it back when we adopted Cribl Stream.” The above quote is from a new Cribl customer talking about why they adopted Cribl Stream to manage observability and security data.
Airline Data Breaches
Travel websites, in particular airlines are key targets for cyberattacks, the reward for compromised data is high in this industry due to the sensitivity of the data involved. Over the years, there have been a number of airline data breaches, with some companies suffering multiple attacks. By analysing some of the major airline and travel attacks over the years and being aware of tactics used by hackers, security procedures can be put in place to prevent attacks.
Secure Supply Chain: Verifying Image Signatures in Kubewarden
After these last releases Kubewarden now has support for verifying the integrity and authenticity of artifacts within Kubewarden using the Sigstore project. In this post, we shall focus on verifying container image signatures using the new verify-image-signatures policy. To learn more about how Sigstore works, take a look at our previous post
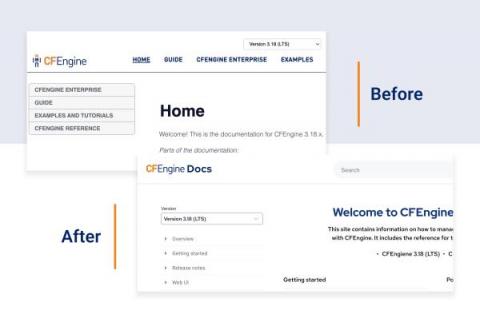
5 improvements coming to the CFEngine Docs
This year, we are improving CFEngine’s ease of use, so it should come as no surprise that we need to rethink our documentation site. For software like CFEngine, great documentation is not just “nice to have”, but a must for our users, both beginners and experienced. CFEngine has helped DevOps teams to automate their day-to-day tasks and make better decisions by providing a holistic overview of their systems.
The Crucial Difference Between IT Security and IT Compliance
What is SaaS Cloud Security and What Are SaaS Security Best Practices?
Uptrends launches new solution for SMS-based 2FA transaction monitoring
As web applications and other digital solutions become more prevalent in everyday life, securing access to these apps against cyber threats becomes more an integral part of their design rather than a separate line of thought. Global cybercrime costs are expected to grow by 15% per year over the next five years, reaching $10.5 trillion annually by 2025.
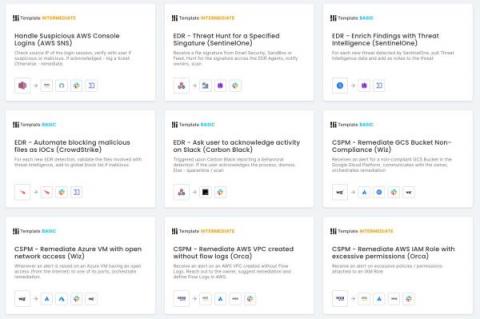
Latest Features Enhance Workflow Creation, Add Modern Controls
The consensus on the state of cybersecurity professionals tends to fall somewhere between “burdened by high volumes of responsibility” and “dangerously understaffed and suffering from unhealthy levels of stress,” depending on how optimistic your source is.