Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
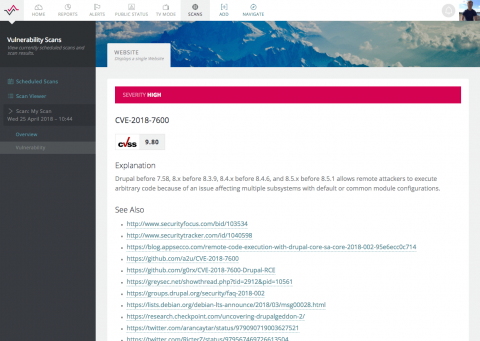
Drupal Security Scanner - Just in Time for Drupalgeddon2
Just as news hits of two highly critical security vulnerabilities in Drupal – a popular open source CMS that powers 4.2% of known CMS websites – we have expanded our external Vulnerability Scanner yet again with Drupal specific security checks. We now offer peace of mind for anyone with a WordPress, Joomla!, SilverStripe or Drupal site, as well as checks for thousands of known software and configuration vulnerabilities for all major software products and operating systems.
Five worthy reads: Data security is taking the world by storm
Information. Data. Personal details. Particulars. Intelligence. Call it what you like—the universal truth is that in the present age, personal data has become one of the most valuable possessions. Companies around the world are scrambling to secure the data they have collected, while those with malicious intentions are vying for these coveted bits of information.
Ransomware attacks continue to rise in 2018
It’s official. Ransomware isn’t just one of the most common types of malware, it is the most prevalent malware used in cyberattacks according to the 2018 Verizon Data Breach Investigations Report (DBIR). This report found that of the data breaches involving malware in 2017, 39 percent made use of ransomware, which was twice the amount used the previous year.
Single Sign-on is here!
We’ve added a new feature we think you’ll want to hear about—Single Sign-on. Uptrends is now compatible with Single Sign-on. Single Sign-on (SSO) is a great way to easily manage user accounts, improve productivity, and improve security, and now you can use SSO with Uptrends.
Connecting the logs with event correlation
Security information and event management (SIEM) helps with managing and analyzing the vast amount of log information generated by networks. Of all the capabilities of SIEM, event correlation is the most powerful. This technique analyzes log data from your servers, applications, routers, firewalls, and other network devices, and identifies patterns of activity that indicate potential attacks.
Not All Hacks Are the Same, Plan Your Network Defenses Accordingly
File Sight Reported Files Read? What Happened?
We sometimes get requests from customers asking for help understanding a File Sight report. It often involves some user account is shown as having read 100’s of files very quickly. This post is to help explain what might have happened.
DevSecOps and Log Analysis: Improving Application Security
As time goes on, more and more organizations are abandoning the outdated waterfall development methodology for more practical and efficient Agile development practices. As this movement has occurred, development teams are moving faster than ever by employing Continuous Integration (CI) and Continuous Deployment (CD) practices that are serving to shorten development cycles and get new features into production with increasing speed.
Five worthy reads: Revolutionizing IT with artificial intelligence
Netflix recommends Stranger Things to you because it knows you like watching sci-fi thrillers. Tinder lets you swipe right into your next date because it’s learned your interests and partner preferences. Amazon keeps showing you Fitbit because you’ve spent a considerable amount of time browsing through the fitness and wellness category.