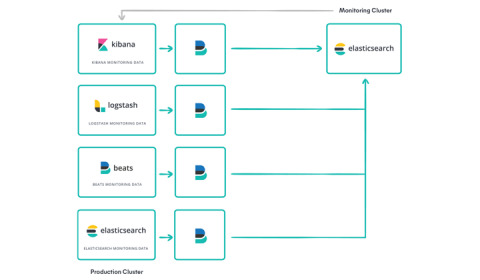
Remove hidden network costs for your logs, metrics, and APM data
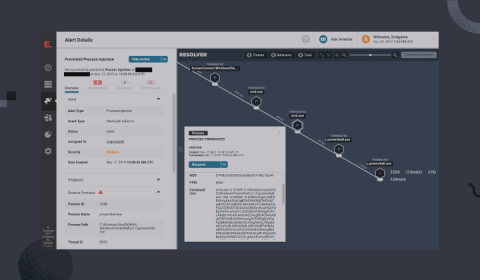
Thousands of customers leverage the official Elasticsearch Service (ESS) on top of Elastic Cloud to get the best experience for running Elasticsearch — including all of Elastic’s exclusive products such as Elastic Logs, Elastic APM, Elastic SIEM, and more.