Operations | Monitoring | ITSM | DevOps | Cloud
Incident Management
The latest News and Information on Incident Management, On-Call, Incident Response and related technologies.
How our product team use Catalog
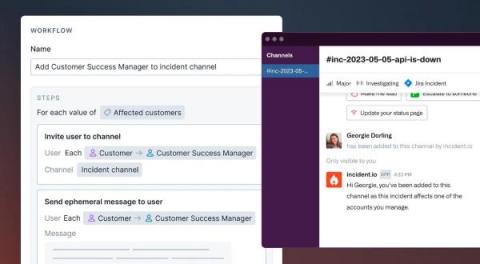
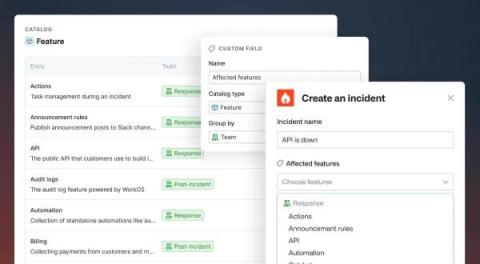
We recently introduced Catalog: the connected map of everything in your organization. In the process of building Catalog as a feature, we’ve also been building out the content of our own catalog. We'd flipped on the feature flag to give ourselves early access, and as we went along, we used this to test out the various features that Catalog powers.
Services are not special: Why Catalog is not just another service catalog
As you may have already seen, we’ve recently released a Catalog feature at incident.io. While designing and building it, we took an approach that’s a tangible departure from a traditional service catalog. Here’s how we’re different, and why.
Azure Incident Management with Escalation Policy
The Unplanned Show, Episode 3: LLMs and Incident Response
incident.io Catalog hands on lab
How AIOps Revolutionizes Observability for TechOps Teams
Managing over 1000 services and applications is daunting for any organization’s IT and Tech operations team. With a diverse mix of on-premises legacy systems and modern cloud stacks, the sheer volume of activity can overwhelm even the most skilled ITOps teams. The task is made more difficult by the fact that observability is fragmented. On average, organizations depend on 21 systems that produce metrics, logs, traces, and alerts for various services.
Squadcast's Improved Mobile App for Better Incident Response
The 2020 pandemic has definitely changed the way teams operate across the globe. Many of you may have already experienced moving from 100% office work to 100% remote work, and now that it has been almost three years since the pandemic started many of us have resorted to hybrid models. We at Squadcast value the importance of efficient communication, reaching the right people during a crisis, and the freedom to resolve critical incidents from anywhere, anytime. Keeping that in mind, we have made major improvements to our mobile app to help you effectively partake in Incident Response activities anytime from across the globe.
Cyberattack Prevention with AI
Cyberattack prevention involves proactive steps organizations take to protect their digital assets, networks, and systems from potential cyber threats. Preventive measures, such as a combination of best practices, policies, and technologies, are employed to identify and mitigate security breaches before they can cause significant damage.
There Are No Repeat Incidents
People seem to struggle with the idea that there are no repeat incidents. It is very easy and natural to see two distinct outages, with nearly identical failure modes, impacting the same components, and with no significant action items as repeat incidents. However, when we look at the responses and their variations, we can find key distinctions that shows the incidents as related, but not identical.