Operations | Monitoring | ITSM | DevOps | Cloud
CFEngine
CFEngine 3.17.0a1-termux - better Android Termux Support
As a follow up to my previous “personal policy” blog I have exciting news: An improved CFEngine is available for Termux!
COVID-19's Impact On Infrastructure Security
It’s no secret that COVID-19 is negatively impacting businesses of all sizes in a number of ways. Some more obvious than others. Unless you are in IT, you’re probably not thinking of how COVID-19 can affect the infrastructure security of your organization, but the truth is that as businesses make the tough decision to layoff employees in order to stay in business, basic security hygiene can easily be overlooked.
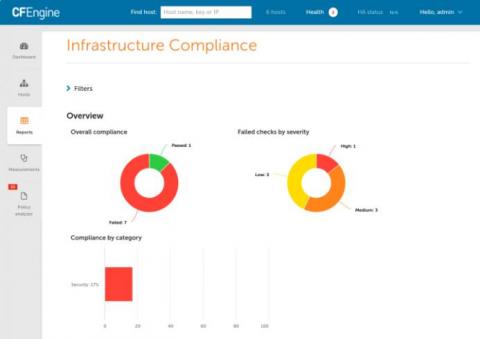
CFEngine 3.16 - Compliance
Today we announce the newest additions to CFEngine. CFEngine 3.16 brings several improvements, bug fixes, and new features. The theme for this release has been compliance, and it notably includes a new category of reports for proving compliance to regulation and other compliance frameworks in high level, easy to read reports. If you are interested to learn more about CFEngine, schedule training, or hear about pricing options, feel free to reach out to us!
How CFEngine stays ahead of the pack
CFEngine was the first Configuration Management solution on the market, and while we have made many and significant changes and improvements to CFEngine in that time, we stay true to the principles that make it such a great product and technology. There are many things that have changed in the market, not at least the competitive situation, we believe that fundamentally many of the challenges stay the same. It then follows that good architecture should not be sacrificed for short term hype.
CFEngine in a High Performance Computing environment
In High-Performance Computing (HPC) uptime and performance are very important. HPC is an area of computing that often focuses on research and development, supporting teams with extremely complex problems they need to solve, and heavy computation mathematical problems, such as protein folding for vaccine development. To achieve this, HPC systems rely on high performance, the equipment is expensive, and the average customer has very high demands.
Introducing cf-secret - Secret encryption in CFEngine
Contributor and CFEngine Champion, Jon Henrik Bjørnstad, developed a tool for encrypting files using CFEngine host keys, called cf-keycrypt. Thank you to Jon Henrik and all of our contributors for helping improve the CFEngine project. Our developer, Vratislav Podzimek, recently took some time to review the cf-keycrypt code, and made many improvements and fixes.
CVE-2019-19394 - Mission Portal JavaScript Injection vulnerability
A vulnerability was recently discovered in CFEngine Mission Portal and has now been fixed. Under certain circumstances, it was possible to inject JavaScript code into data presented in Mission Portal, that would be run in the user’s browser. This security issue was fixed in CFEngine 3.10.7, 3.12.3, and 3.15.0, and will be mitigated by upgrading your hub to one of these versions (or later). No other action is required than upgrading the Hub.
CFEngine 3.12.4 and 3.15.1 released
We are today very excited to bring you new updates to CFEngine. This is a set of patch releases for the CFEngine 3.12 LTS and 3.15 LTS series. We usually release new patch releases every 6 months, but we want to bring new features and all improvements and bug fixes to our users as soon as possible.