Operations | Monitoring | ITSM | DevOps | Cloud
Security
The latest News and Information on CyberSecurity for Applications, Services and Infrastructure, and related technologies.
Detecting Malware and Watering Hole Attacks with Splunk UBA
You may be surprised to learn that a particular malware is responsible for data theft in over 20% of financial institutions and other verticals in 2019. Watering hole attacks involve a web server that hosts files or applications where the website or files on the site become weaponized with malware. While recent news cycles have shined a spotlight on ransomware and crimeware, malware is not a new concept.
Protect Your AWS Infrastructure with GuardDuty and Coralogix
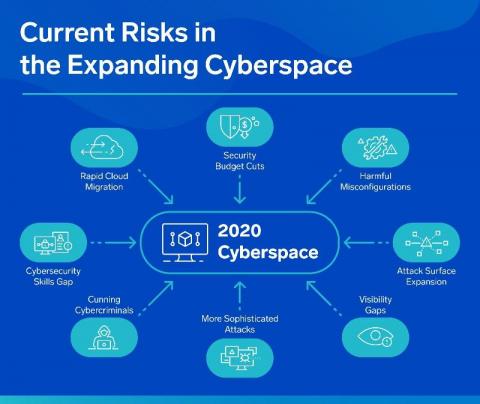
Cloud environments like AWS can be a challenge for security monitoring services to operate in since assets tend to dynamically appear and disappear. Making matters more challenging, some asset identifiers that are stable in traditional IT environments like IP addresses are less reliable due to their transient behavior in a cloud service like AWS. Amazon GuardDuty protects your AWS environment with intelligent threat detection and continuous monitoring.
How to use Kibana effectively. Today: Detect possible frauds in your data
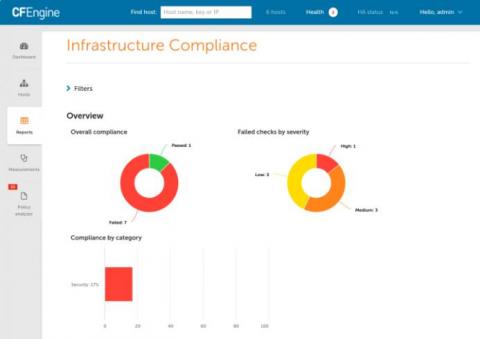
CFEngine 3.16 - Compliance
Today we announce the newest additions to CFEngine. CFEngine 3.16 brings several improvements, bug fixes, and new features. The theme for this release has been compliance, and it notably includes a new category of reports for proving compliance to regulation and other compliance frameworks in high level, easy to read reports. If you are interested to learn more about CFEngine, schedule training, or hear about pricing options, feel free to reach out to us!
The Importance of Monitoring SSL Certificates
Secure Sockets Layer, or SSL, is a global security standard technology that is being adopted by a number of different organizations across the globe. Essentially, SSLs are small data files containing a cryptographic key. This key carries important information about the organization using it. Around 600,000 websites have installed SSL certificates for security.
VPN vs. Remote Desktop - Gateway Security Concerns
VPNs and Remote Desktop Gateways are two different tools used to achieve similar goals. That is: access content or software remotely and securely, and improve the overall freedom of the user – whether that’s from prying eyes or the need to have physical access to their business network. But while each option can be attractive, neither is without its security concerns.
3 ways secrets management improves monitoring & observability
Monitoring — by its very nature — requires privileged access to internal and external services. In order to safely maintain visibility into critical systems, it’s vital to have some form of secrets management to manage authentication credentials (AKA, "secrets"), including passwords, keys, APIs, tokens, and any other sensitive pieces of information in your IT infrastructure.
Automating Security on Your Observability Platform: Cortex XSOAR & Logz.io
Managing a complex microservice-based architecture requires defending multiple endpoints. Automating security covers a vast amount of tools and methodologies, so making sure they all communicate is critical. Additionally, tool sprawl in any aspect of DevOps requires putting automation to good use. The Logz.io Cloud SIEM focuses on identifying threats. To optimize its effectiveness, we have negotiated and built out multiple integrations tying complementary tools together.